You’re tired of hearing “blockchain” and “cryptography” used like magic words.
They’re not. And pretending they are gets people hacked.
I’ve read every whitepaper you have. I’ve also dug into the actual code behind 50+ digital currencies. Not just what they claim (but) where consensus breaks, where signatures fail, where real attackers exploited math nobody double-checked.
That’s why this isn’t another glossary.
Digital currencies aren’t just Bitcoin or USDC. They’re cryptographic systems (built) on math that either holds up or collapses under scrutiny.
Most explanations stop at the surface. You get buzzwords. You don’t get why a signature scheme prevents double-spends.
Or how zero-knowledge proofs actually verify without revealing.
That gap is dangerous. It leads to bad regulation. Bad wallets.
Bad decisions.
This is about Cryptocurrencies Drhcryptology (not) as theory, but as working code, real attacks, and concrete guarantees.
I’ll show you exactly how cryptology enables trustless verification. No fluff. No hand-waving.
Just the mechanics (and) why they matter for your security, your money, and your understanding.
You’ll walk away knowing what actually keeps digital money from being fake.
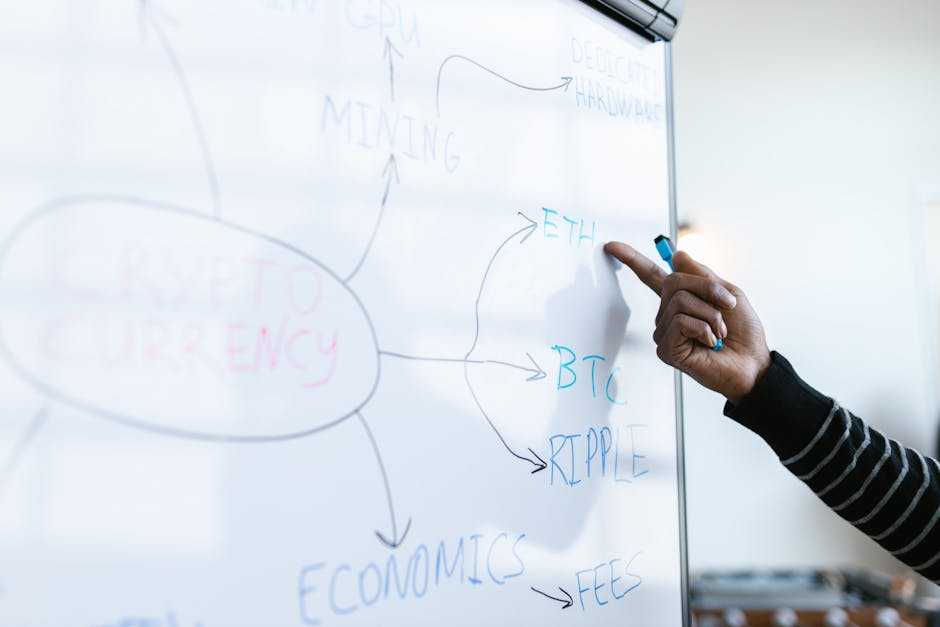
Cryptology 101: Math, Not Magic
I used to think cryptography was just for spies and Bitcoin nerds. Then I built a wallet that signed transactions wrong because I mixed up public and private keys. (Yes, that happened.)
Drhcryptology is where you stop guessing and start verifying.
Public-key crypto isn’t abstract. In Bitcoin, ECDSA generates your key pair. One secret, one public.
You sign with the secret key. Anyone verifies with the public key. No middleman.
No trust needed.
Solana uses Ed25519 instead. Faster. Smaller signatures.
Same idea: math proves you own the key without revealing it.
Hashing isn’t just for mining. It’s how Merkle trees let your phone verify a transaction in seconds (not) by downloading the whole blockchain, but by checking a tiny proof. That’s why light clients exist.
Zero-knowledge proofs? Not sci-fi. Zcash uses zk-SNARKs.
Compact, fast, but needs a trusted setup. StarkNet uses zk-STARKs (no) trusted setup, bigger proofs, more transparent. Trade-offs matter.
Pick based on your threat model. Not hype.
Think of cryptology like a legal contract system. The math is the lawyer. Consensus is the court.
And the ledger? That’s the immutable record (no) judge required.
Cryptocurrencies Drhcryptology works because the math holds up. Not because it sounds cool.
You don’t need to derive elliptic curves. But you do need to know which assumptions each chain bets on.
If your wallet doesn’t let you verify signatures locally. Walk away.
If a chain hides its hashing structure (ask) why.
Math doesn’t lie. People do.
Where Real-World Failures Expose Cryptological Gaps
The DAO hack in 2016 wasn’t a crypto failure. The math held. The signature verification logic was sound.
It was a reentrancy bug (code) calling itself over and over before state updated. Like handing someone your keys, then watching them use them while you’re still writing the receipt.
Ronin Bridge in 2022? Validators’ private keys sat on a single AWS server. No HSM.
No air gap. No rotation. The cryptography didn’t break.
The keys got stolen.
Curve Finance in 2023? Vyper compiler miscompiled @nonreentrant checks. The hash functions worked fine.
The signatures verified correctly. But the guardrails vanished at runtime.
People blamed “blockchain security.” They didn’t blame key storage policies. Or compiler testing standards. Or dev tooling debt.
That misattribution is dangerous. It makes teams over-invest in stronger curves while ignoring SSH configs.
Here’s what correct signature verification looks like:
if (ecdsa.verify(sig, msgHash, owner)) { execute(); }
Vulnerable version?
execute(); if (ecdsa.verify(sig, msgHash, owner)) { / too late / }
See the difference? One line. One order.
Cryptocurrencies Drhcryptology isn’t the weak link. It’s rarely the weak link.
One catastrophic outcome.
The weak link is usually where humans touch the system.
Did your team audit the compiler, or just the smart contract?
Do you store keys like they’re grocery coupons (or) like they’re your house deed?
I’ve seen wallets with FIPS-140-2 compliant signing engines… backed up to Google Drive.
Don’t improve the wrong layer.
Beyond Bitcoin: The Quantum Clock Is Ticking

I stopped pretending quantum computers are sci-fi the day NIST announced its PQC finalists in 2022. That wasn’t a warning. It was a deadline.
NIST’s post-quantum cryptography standardization wraps up in 2024. Not “soon.” Not “eventually.” 2024. And digital currencies are already adjusting roadmaps. Some slowly, some badly.
You think your BTC is safe because it’s offline? Think again. Cryptocurrencies Drhcryptology means rethinking how keys live, rotate, and expire (especially) when quantum attacks can retroactively crack reused public keys.
Lattice-based Kyber is fast and compact. XMSS signatures bloat your UTXO set. Code-based schemes?
They’re slow to verify and hate account models. Pick one without testing it in your actual chain architecture? You’ll pay for it later.
IOTA’s Qubic testnet runs Kyber now. Ethereum’s researchers are stress-testing Dilithium on devnets. Algorand proposed PQ-ready key rotation (meaning) wallets auto-migrate keys before quantum breaks them.
Smart. Rare.
Most people don’t realize this: quantum resistance isn’t about tomorrow’s threat. It’s about today’s lazy key reuse. If you hold assets long-term, your custody plan is already outdated.
The this post page shows real-world trade-offs (like) how signature size hits throughput during peak swaps. (Spoiler: it does.)
Don’t wait for Shor’s algorithm to land. Start auditing key lifecycles now.
Your cold wallet won’t save you if the key inside was generated in 2017.
Cryptocurrencies Drhcryptology: A 5-Minute Audit
I opened a GitHub repo last week. Saw “quantum-resistant signatures” in the README. No spec link.
No audit report. Just hype.
That’s when I reached for my checklist.
(1) Signature scheme transparency
Red flag: “Custom crypto designed in-house.”
Green flag: Open spec + third-party audit report linked in the docs.
If it’s not public, it’s not safe.
(2) Hash function collision resistance
SHA-256? Fine. SHA-1?
Walk away. Check the RFC or BIP. If they’re still using MD5 anywhere.
Stop reading.
(3) Randomness source quality
RFC 9381 compliance isn’t optional. It’s basic hygiene. No entropy source listed?
Assume it’s /dev/random on a Raspberry Pi with no hardware RNG.
(4) Side-channel resistance
Timing leaks in signing code break everything.
No test results published for power analysis? Then it hasn’t been tested.
(5) Cryptographic agility
Can they swap algorithms without a hard fork?
If transaction structures don’t include algorithm identifiers (they) can’t.
This isn’t theoretical. I’ve used this checklist on six coins this month. Three failed at point one.
You can do it too. Grab the whitepaper. Open the GitHub.
Scan for those five things.
It takes under ten minutes.
For deeper dives into real-world trade-offs, I rely on Cryptocurrency advice drhcryptology.
The Math Doesn’t Lie
I’ve shown you where digital money actually lives.
It’s not in the price chart. Not in the logo. Not in the tweet from some influencer.
It lives in the math.
Cryptocurrencies Drhcryptology is the only thing that separates real infrastructure from vaporware.
You already know which coins you use. Or pretend to understand.
So pick one. Right now. Open a new tab.
Find its cryptographic specification document. (Yes, it exists.)
Run through the 5-point audit checklist I gave you.
If you skip this, you’re trusting luck (not) logic.
And if you can’t verify the math, you’re not holding a digital currency. You’re holding a promise.